Hack of NSA ‘cyber weapons’ verified by Snowden docs – report
Published 19 Aug, 2016 23:54 | Updated 20 Aug, 2016 12:47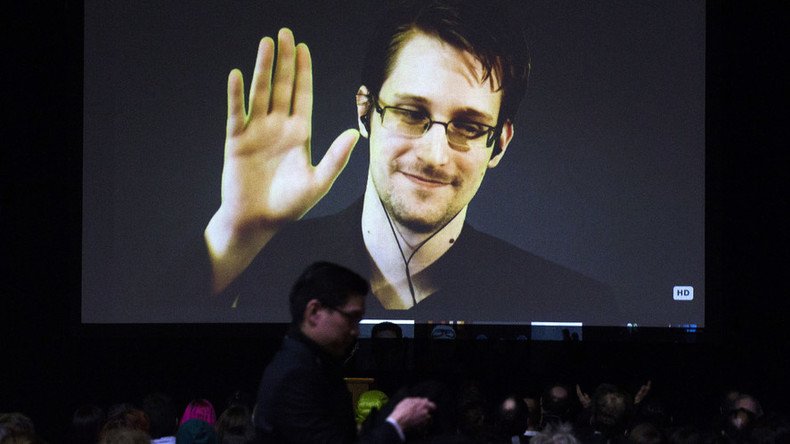
Newly liberated NSA files from whistleblower Edward Snowden remove any doubt that the “ShadowBrokers” hack on the NSA this week is real, according to a new report.
Following Snowden’s reactions on Twitter the day after an apparent hack on the National Security Agency, the publication that formed specifically around his 2013 NSA leaks revealed more documents never before seen in public view.
The Intercept’s report finds that the NSA malware uncovered by the “ShadowBrokers” hack on Monday “is covered with the NSA’s virtual fingerprints and clearly originates from the agency.”
While Snowden suspects a “rival” of the NSA is responsible, no one knows for sure. However, a Johns Hopkins University cryptographer, Matthew Green, told the Intercept the software “exploits” now out in the open present a two-fold risk. “First, that the person or persons who stole this information might have used them against us,” and secondly, “that ordinary criminals will use them against corporate targets.”
READ MORE: NSA malware menace: ‘If device is connected to internet, it can be broken into’
“If this is indeed Russia [behind the Shadowbrokers hack],” Green said, “then one assumes that they probably have their own exploits, but there’s no need to give them any more.”
“This is the equivalent of leaving lockpicking tools lying around a high school cafeteria,” Green added. “It’s worse, in fact, because many of these exploits are not available through any other means, so they’re just now coming to the attention of the firewall and router manufacturers that need to fix them, as well as the customers that are vulnerable.”
Among the “cyber weapons” seized and put up for auction by ShadowBrokers, is an array of systems and programs that clandestinely nestle into computers across the globe, according to the Intercept.
The centrally cited Snowden document that all but confirms the recent hack is real is an NSA top-secret manual on how to attack computers and their networks with malicious software. In the document obtained in 2013, but released only on Friday, instructions include a 16-character sequence NSA agents would use to track their malware, “ace02468bdf13579,” which also happens to be found repeatedly in the ShadowBrokers revelatory documents on the government surveillance program called SECONDDATE.
READ MORE: NSA website down for 1 day after hackers take out its affiliate – media
SECONDDATE was part of a “complex global system” that infected millions of computers worldwide, one government document estimated, according to the Intercept.
The infection actually came from an NSA web server, but SECONDDATE was integral in redirecting targeted web browsers there, and it did so by capturing web requests, a “man in the middle” style cyberattack.
The ShadowBrokers hack offers for the first time “a glimpse at how an elaborate system outlined in the Snowden documents looks when deployed in the real world,” the Intercept reported, adding that the newly released Snowden documents show how SECONDDATE was used to spy on Pakistan and a computer system in Lebanon.












