Tor anonymizer network among NSA’s targets, Snowden leaks reveal
Published 4 Oct, 2013 15:04 | Updated 6 Oct, 2013 18:43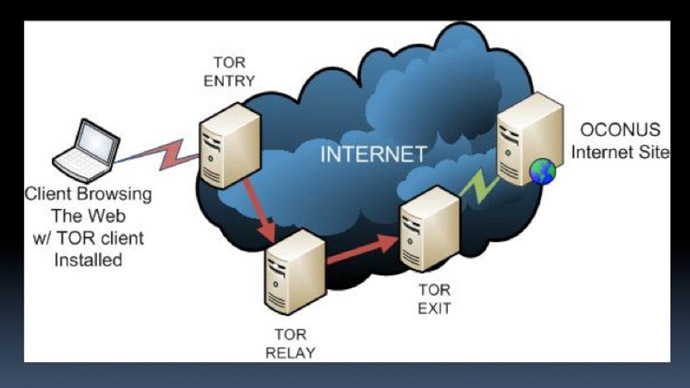
Top-secret national security documents disclosed to the Guardian by Edward Snowden show United States and British intelligence have long attempted to crack the Tor anonymizer network used by human rights workers, journalists, cybercriminals and others.
On Friday, the Guardian published leaked documents attributed to the former intelligence contractor revealing how the US National Security Agency and Britain’s Government Communications Headquarters, or GCHQ, have worked extensively towards compromising the computers of people who browse the Internet with Tor, a program that routes traffic through multiple nodes in an effort to help mask the identities of its users.
According to the Guardian’s James Ball, Bruce Schneier and Glenn Greenwald, the NSA’s “current successes against Tor rely on identifying users and then attacking vulnerable software on their computer.”
“While it seems that the NSA has not compromised the core security of the Tor software or network, the documents detail proof-of-concept attacks, including several relying on the large-scale online surveillance systems maintained by the NSA and GCHQ through internet cable taps,” the writers add.
The Guardian has so far published three top-secret government
slideshows used to discuss the Tor network and possible
vulnerabilities that might compromise users if properly
exploited.
In one document, the NSA notes that Tor, or “The Onion Router,” enables anonymous Internet activity to Iranian and Chinese dissidents, terrorists and “other targets too!” The software has become increasingly used around the globe by privacy-minded individuals of all sorts in recent months. However, previous documents disclosed by Mr. Snowden detailed how the intelligence community have made many successful efforts to compromise other would-be secure modes of communicating.
As RT reported previously, the number of Americans using Tor jumped 75 percent between June 1, just days before the first Snowden leak, and August 27, 2013.
One government document, “Peeling Back the Layers of TOR with Egotisticalgiraffe,” suggests the security of some Tor users can be compromised if the government or other malicious actor can exploit bugs in the Firefox browser and other vulnerabilities.
In another slideshow, “Tor Stinks,” the government claims it already has access to a select number of nodes which anonymized traffic is navigated through.
The “goal,” according to the NSA slide, is to “expand [the] number of nodes we have access to.” To accomplish as much, it’s acknowledged that GCHQ runs Tor nodes under a program of its own, and that other partners may be able to assist with further efforts to deconstruct traffic patterns to narrow-in on otherwise anonymous users.
Other tools used by the NSA involve collecting cookies from Tor users created when they are browsing the Web without the anonymizer software running. One technique, codenamed “QUANTUM,” exists to degrade, deny and disrupt Tor access, according to the documents. Another, “QUANTUMCOOKIE,” “forces client to divulge stored cookies” which could then further aid investigators attempting to hone in on targets otherwise protected by Tor.
Despite the NSA and GCHQ’s efforts, though, Tor itself has proved to be invincible to government attacks thus far.
“Can we exploit nodes? Probably not,” reads one slide which cites “legal and technical challenges.”
Still, the government has considered disrupting traffic over the Tor network to likely draw users off the nodes and into a habitat where their actions could be more easily traced. In one slide, the NSA suggests they could “set up a lot of really slow Tor nodes,” disguised as high bandwidth, “to degrade the overall stability of the network.”
Tor documents, courtesy of Glenn Greenwald: