Revealed: How governments can take control of smartphones
Published 25 Jun, 2014 01:32 | Updated 27 Jun, 2014 14:14
‘Legal malware’ produced by the Italian firm Hacking Team can take total control of your mobile phone. That’s according to Russian security firm Kaspersky Lab and University of Toronto’s Citizen Lab(which also obtained a user manual).
Operating since 2001, the Milan-based Hacking Team employs over
50 people and offers clients the ability to “take control of your
targets and monitor them regardless of encryption and mobility,"
while “keeping an eye on all your targets and manage them
remotely, all from a single screen.”
It’s the first time Remote Control Systems (RCS) malware has been
positively linked with mobile phones and it opens up a new
privacy threat potential to mobile phone users.
“Our latest research has identified mobile modules that work on all well-known mobile platforms, including as Android and iOS,”wrote Kaspersky researcher Sergey Golovanov.
“These modules are installed using infectors – special executables for either Windows or Macs that run on already infected computers. They translate into complete control over the environment in and near a victim’s computer. Secretly activating the microphone and taking regular camera shots provides constant surveillance of the target – which is much more powerful than traditional cloak and dagger operations.”
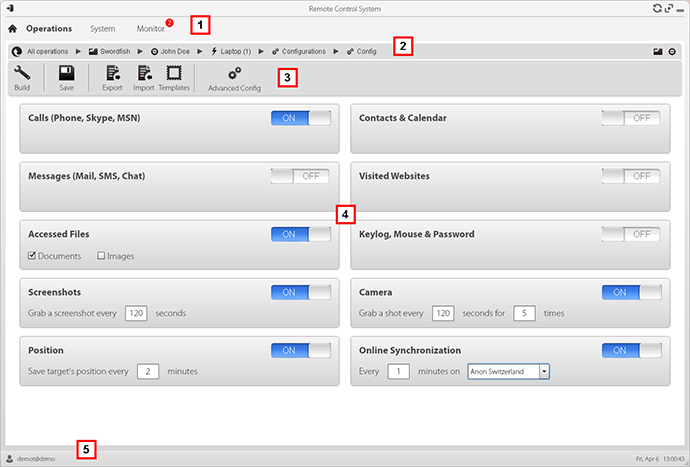
Police can install the spy malware directly into the phone if there is direct access to the device, or if the owner of the phone connects to an already infected computer, according to Wired.
Various softwares can also lure users to download targeted fake apps.
Once inside an iPhone, for instance, it can access and activate all of the following: control of Wi-Fi, GPS, GPRS, recording voice, e-mail, SMS, MMS, listing files, cookies, visited URLs, cached web pages, address book, call history, notes, calendar, clipboard, list of apps, SIM change, live microphone, camera shots, support chats, WhatsApp, Skype, and Viber.
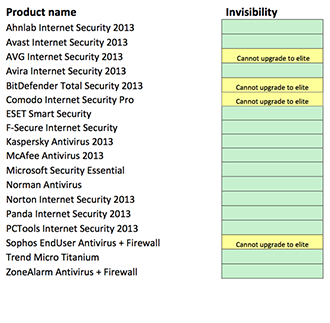
While the malware can be spotted by some of the more sophisticated anti-virus software, it takes special measures to avoid detection – such as “scouting” a victim before installation, “obfuscating” its presence, and removing traces of its activity.
Hacking Team has maintained that its products are used for lawful governmental interceptions, adding that it does not sell items to countries blacklisted by NATO or repressive regimes.
Wired reported that there have been cases where the spying apps were used in illegal ways in Turkey, Morocco, and Saudi Arabia.
Citizen Lab discovered spying malware hiding in a legitimate news app for Qatif Today, an Arabic-language news and information service that reports on events in Saudi Arabia's eastern Qatif region. It also argued that circumstantial evidence pointed to Saudi Arabia’s government using the spying malware against Shia protesters in the area.
“This type of exceptionally invasive toolkit, once a costly boutique capability deployed by intelligence communities and militaries, is now available to all but a handful of governments. An unstated assumption is that customers that can pay for these tools will use them correctly, and primarily for strictly overseen, legal purposes. As our research has shown, however, by dramatically lowering the entry cost on invasive and hard-to-trace monitoring, the equipment lowers the cost of targeting political threats for those with access to Hacking Team and Gamma Group toolkits,” Citizen Lab said in its report.
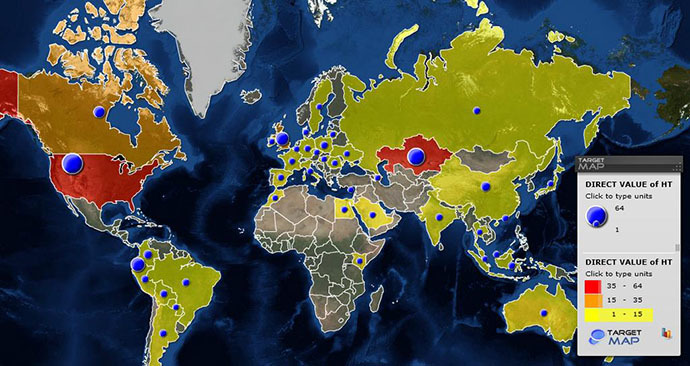
Hacking Team controls the spying malware remotely via command-and-control servers. Kaspersky has discovered more than 350 such servers in more than 40 countries. A total of 64 servers were found in the US – more than in any other country. Kazakhstan came in second, with a total of 49 servers found. Thirty-five were found in Ecuador and 32 in the UK.












