Stuxnet no threat to Iranian nuclear program
Published 17 Jan, 2011 11:49 | Updated 18 Jan, 2011 15:25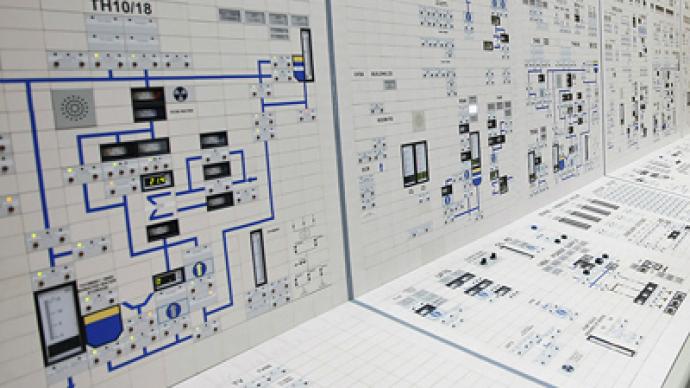
Western media claims Russian scientists who provide technical assistance at Iran's Bushehr reactor have raised concerns about the plant's computer damage caused by the Stuxnet virus.
The computer worm is believed to be a result of a sophisticated joint US-Israeli cyber attack.The nuclear experts have reportedly urged the Kremlin to postpone the plant's activation, warning of another Chernobyl-style nuclear disaster.Vladimir Sotnikov from the Moscow-based Institute of World Economy and International Relations points out that all modern nuclear facilities maintain double systems to prevent nuclear disasters, so even if the facility’s computer system is infected with a worm, the newly-built Bushehr power plant is certainly not under any threat.Sotnikov admits that some intelligence services, probably Israeli and American, could have taken joint measures to undermine Iran’s nuclear ambitions.In any case, he expressed the opinion that there will be no more delays in finishing the Bushehr nuclear power plant.“Russia in no way assists in any military dimension of the Iranian nuclear program,” Sotnikov said.Stuxnet is believed to be the most advanced and complex cyberweapon ever produced. It began spreading around the word in mid-2009, turning up in different industrial programs, however at that time it was unexplained.In recent days The New York Times has reported on Israel testing the Stuxnet worm at its heavily-guarded Dimona complex, allegedly being a part of joint American and Israeli efforts to postpone Tehran’s creation of its own nuclear bomb. The research has been going on for over two years.According to experts, at Dimona the exact same nuclear centrifuges as the ones that are a part of Bushehr reactor were used to work on the virus. “To check out the worm, you have to know the machines,” said an American expert on nuclear intelligence, as cited by the New York Times “The reason the worm has been effective is that the Israelis tried it out.”Russia’s Kaspersky Laboratory experts believe that so called zero-day computer vulnerabilities were used in the Stuxnet attack. The experts note that creators of the worm had deep knowledge of SCADA – a technology used in monitoring and controlling industrial, infrastructure and service processes on oil pipe-lines, electric power plants, major communication systems, airports, vessels and military facilities all over the world. After dissecting the worm’s code, the Kaspersky Lab gave its verdict: that the main goal of Stuxnet worm is not espionage or gathering information from “infected” systems, its main objective is to cause harm.“Stuxnet is not stealing money, it does not send spam and it does not collect confidential information. This worm is created to literally control huge production capacities,” wrote Kaspersky Lab CEO Evgeny Kaspersky in his blog. This worm has two functions. One of them makes the centrifuges to spin wildly out of control, tearing themselves apart, when the second part of the worm actually plays back to the plant operators pre-recorded readings, that were gathered when centrifuges were operating normally. The attack was not fully successful, some of the Iranian centrifuges stopped operations, while the other survived. However it is not clear, whether the attacks will continue. According to experts who looked into the Stuxnet code, further attacks and versions of the worm are possible.However, Russia’s Rosatom state corporation spokesman Sergei Novikov denies that there are any viruses endangering the security of the Bushehr nuclear power plant. "There are no viruses in the power plant's computer network, especially in units responsible for security, because this network is totally autonomous and isolated from external sources," he said, as cited by Interfax.
Anton Khlopkov, editor in chief of a nuclear energy publication, says although the potential threat should be studied – a Chernobyl-style scenario nowadays is in the realm of fiction.“Since Chernobyl, the safety of the reactors has been improved significantly. Most of the safety systems are backed up by another one and usually [the reactors] are quite well protected. Just as a cyber terrorist could not damage such a high-tech facility,” he said.
The chief technical officer for Positive Technologies, specializing in information security, Sergey Gordeychik believes that using computer viruses for industrial espionage can be called a trend of the new century. “Stuxnete’s peculiarity is that aside from spy functions, it also has mechanisms aiming at subversive operations, which can inflict physical damage in the real world. To draw a parallel, Stuxnet in the real world would simultaneously be a spy and a terrorist,” Gordeychik says.He estimates the possible cost of creating Stuxnet to range from $600,000 to one million dollars. “However, one should take into account not only program development, but also intelligence costs. The virus has been thoroughly tested with expensive Siemens equipment and emulators. It exploits 0-day vulnerabilities of Windows and Siemens Simatic WinCC that have been unknown to others, as well as digital certificates obtained through industrial espionage,” he says. “Taking into account Stuxnet’s technical characteristics, how widespread it is in Iran, the peculiarities of the detrimental module and a number of other factors, an attack by a state with high scientific and technological potential looks like the only possible scenario,” Gordeychik added.The fears of possible damage to the Bushehr NPP were first voiced in October, when the worm was detected in its system. The subject was once again raised on Monday, 17 January, when the UK’s Daily Telegraph newspaper cited the concerns of unnamed Russian scientists who are reportedly providing assistance with Iran’s attempts to activate the country’s first nuclear power plant.











